-
Posts
4,129 -
Joined
-
Last visited
Contact Methods
-
Twitter
https://twitter.com/alpenwater
- Website URL
Profile Information
-
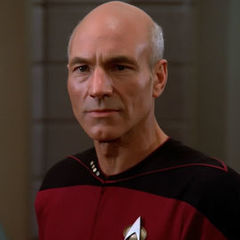
Gender
Male
-
Location
Switzerland
-
Interests
all things mechanical, PC's, Unixes, hiking, camping, history, paleontology, biology, movies
-
Biography
born (1985) -> school -> army (Lt, Infantry) -> work (logistics, web dev) -> electrical engineering
-
Occupation
Electrical Engineer (DSP, Embedded Systems)
-
Member title
2CPU Enthusiast
System
-
CPU
2 × Intel Xeon X5680 (6C/12T per CPU), 3.33 GHz
-
Motherboard
EVGA SR-2
-
RAM
24 GB Corsair Dominators 1866 MHz
-
GPU
GTX Titan & GTX 780
-
Case
Caselabs SMH10
-
Storage
40-ish TB server w/ ZFS
-
PSU
Enermax Platimax 1200 W
-
Display(s)
Dell 24" 1920x1200
-
Cooling
2 × XSPC Raystorm Copper, MIPS block for EVGA SR-2, 2 × Aquacomputer Titan, 2 × HWLabs SR-1 560 mm, 2 × Alphacool Dominator RAM blocks, 2 × D5, 1 × Alphacool XT45 480 mm, Aquacomputer Aqualis
-
Keyboard
QPAD MK85 w/ Cherry Blues
-
Mouse
Wacom Intuos
-
Sound
Yes
-
Operating System
Arch Linux
Recent Profile Visitors
alpenwasser's Achievements
-
Where are ya?
-
-

You can check your stats in the Web Control in Folding@home. If you click on user stats it will take you to your stats page.
You can also check on extremeoverclocking.com. Your stats page is here. https://folding.extremeoverclocking.com/user_summary.php?s=&u=1040987There's a list of the requirements for each badge here and also where you can request a new badge:
You have met the requirements for the contributor badge and I've added it to your profile

It'll also show up next to your username & profile picture when posting on the forums (desktop). If you click the award it will take you to your extremeoverclocking stats page.

-
-

Looking for new BOINC Team Leader
alpenwasser replied to alpenwasser's topic in Folding@home, Boinc, and Coin Mining
Alright, @Ithanul, you're it! There are no special powers with your badge except bragging rights. Have fun! -
Stuff should be updated now. Been moving apartments in the past two weeks and had to wait for Internet! The Horror! I'll happily relinquish the BOINC leader position (can't comment on F@H), there's another thread for that after all, but the badge assigning unfortunately has to be done be an account with moderator privileges. But yes, while I do still regularly pop in here (mostly for behind-the-scenes stuff and things like this), I'm not around enough for now that it makes much sense for me to be BOINC team leader. But I think there might have been a miscommunication -- the idea of the thread was that other mods can process the requests too, not just me. That's the whole point! My bad -- I'll communicate that to the others more clearly so that you young grasshoppers can get your badges more quickly in the future.
-
Since the primary two mods responsible for badge assignment duties (Whiskers and myself) haven't been around much in recent months, we've had a bit of a chat behind the scenes and thought we'd try something new. Instead of you having to try to figure out which mod to write a PM to in order to get your badges, we're gonna try to collect all requests in a single thread and then whichever mod sees it first can assign the badges. DON'T FORGET TO GIVE YOUR FOLDING ID AND/OR ACCOUNT ON BOINCSTATS SO THAT WE CAN VERIFY YOUR STATS! F@H Badge Thresholds In order to be rewarded with the Folding @ Home badge, please note the following requirements. (subject to change, updated Jan 1st 2021) Contributor - When you have contributed more than 5 Million Points, you will qualify for this badge, to show your commitment to LTT and the team. Bronze Contributor - When you have contributed more than 25 Million points, you will qualify for this badge. This reflects your serious support of the team. Silver Contributor - When you have contributed more than 100 Million points, you will qualify for this badge. This reflects your serious and continued support of the team. Gold Contributor - When you have contributed more than 500 Million points, you will qualify for this badge. This reflects your dedication and continued support of the team and your very generous donation of resources. Platinum Contributor - When you have contributed more than 1 Billion points, you will qualify for this badge. This reflects your dedication and continued support of the team and your very generous donation of resources. You are now a legend! Diamond Contributor - When you have contributed more than 2.5 Billion points, you will qualify for this badge. This reflects your insane dedication and continued support of the team and your extreme donation of resources. Tales of your folding adventures will be whispered through the ages; you are now mythical. F@H Event Badge Thresholds These are special badges handed out for participating in the official Folding events organized by the Folding community. These badges will be handed out automatically after the events to eligible participants (subject to individual event guidelines and requirements). Event Founder - A unique badge only available to those who participated in the first event. ** This Badge is no longer available for distribution ** Event Newbie - For participating in at least 1 Folding event. Event Veteran - For participating in at least 3 Folding events. Event Fanatic - For participating in at least 5 Folding events. Below is the list of Official Folding Events that have counted toward the Folding Event badges. To be an Official Folding Event, they must specifically be endorsed by LMG, so Folding Events like the Summer Sprint of 2019 do not count towards obtaining these badges. Additionally, on top of folding and meeting the minimum requirements for the event, you must make sure you sign up specifically to be tracked for the event; we do not track every LTT user who was folding at the time of the event (this has caused a lot of confusion in the past). BOINC Badge Thresholds In order to be rewarded with the BOINC Team badge, please note the following requirements. (subject to change) Contributor - When you have contributed more than 25,000 credits, you will qualify for this badge, to show your commitment to LTT and the team. Bronze Contributor - When you have contributed more than 1 Million credits, you will qualify for this badge. This reflects your serious and continued support of the team. Silver Contributor - When you have contributed more than 25 Million credits, you will qualify for this badge. This reflects your serious and continued support of the team and your very generous donation of resources. Gold Contributor - When you have contributed more than 100 Million credits, you will qualify for this badge. This reflects your dedication and continued support of the team and your very generous donation of resources. You are now a legend! BOINC Event Badge Thresholds These are special badges handed out for participating in the official BOINC events organized by the forum's BOINC community. These badges will be handed out automatically after the events to eligible participants (subject to individual event guidelines and requirements). BOINC Event Newbie - Participate in at least 1 BOINC event. BOINC Event Regular - Participate in at least 4 BOINC events. BOINC Event Enthusiast - Participate in at least 8 BOINC events. BOINC Event Fanatic - Participate in at least 10 BOINC events. Note on Processing We haven't nailed down all the details yet, so this might change as things evolve, but to make it easier for us to track which requests have been processed and which have not, we're going to set posts which have been processed to Hidden for now. So don't be scared if the thread appears empty to you, that might just mean we're all caught up on badge assignment duty. Team Membership To be eligible for the badges, you have to have contributed the credits/WUs under the LTT team membership. The teams are: https://stats.foldingathome.org/team/223518 for F@H, and https://www.boincstats.com/stats/-1/team/detail/b85bbff1c6df413a4b44cfb82854273f for BOINC Happy crunching! New Official F@H FAQ & Guide.
-
Yeah I think he's had the same problem as me -- meatspace getting in the way. I can do the badges too; both of yours should now be upgraded.
-
Apologies for the delay -- I was away on meatspace business in recent months. Like the idea, added the pictures. Thanks for the suggestion!
-

Looking for new BOINC Team Leader
alpenwasser posted a topic in Folding@home, Boinc, and Coin Mining
Hello folks! So, as many will undoubtedly have noticed, I haven't been super active on the forums in recent times (sorry about that -- extremely busy in meatspace life with job and such stuff). Even more terribly, I have not actually been generating BOINC credits (that one has more to do with my current living situation which doesn't allow for 24/7 number crunching). I know, I know, an egregious blunder on my part. So one of our members contacted us and asked if maybe we would want to choose a new BOINC team leader who's actually, you know, active. The selection process will be as follows: - Y'all can nominate people, including yourselves, in this thread. - If need be, we'll have a vote. - We (the mods) reserve the right for final approval/veto/tossing our own votes into the hat. What will the winner get? This here fancy badge: Your duties will mostly be ... what you make them, to be honest. Cheers, -aw -
The dude seems like he has some serious anger issues.
-
I see, thanks for that link. I think the trouble with meritocracy here is what people understand it to mean, and how much importance they place on it. Most people I have talked with about the topic have focused very heavily on technical skills, neglecting or even entirely omitting social skills. That's also why I have been somewhat conditioned to it being a red flag for me, and I'll usually try to steer clear of environments which are obsessed with it. If somebody defines merit so narrowly, and then places it above anything and all else, I'm going to have to disagree with that. As you yourself said: People skills matter a lot. If we define merit more broadly, to encompass many more aspects of the human experience, sure, it might become more useful. But even then ... who decides what merit is, and how? Certainly, there are many metrics you can measure, but how to decide which metrics matter, and how much? And yes, you can notice if somebody has good people skills (or rather: somebody can convince you that they have), but it's not like you can just grade that and give them a 8/10 and that's a truly objectively correct measurement. And even in cases where clear metrics exist, how often and how rigorously are they actually applied by the decision-makers? You might be able to measure contribution frequency, compile times and execution speed, but when it comes to things like legibility, commenting quality and beauty of code, things are suddenly more subjective. But are those criteria irrelevant? At least to me, they're not. Your mileage may admittedly vary. So as soon as you have things like that being taken into account (and I think they should be -- people may disagree with me on that, fair enough), you suddenly no longer have a truly objective measurement of a person's merit (and I think objectivity is a goal of a meritocracy, at least for the people with whom I have so far talked about this in my life). People contributing to different parts of a project under different supervisors will not be judged equally because they're not judged by the same people. I mean, just look at this forum: Sure, us moderators try to make the user experience as uniform as possible by talking to each other about problem cases and warnings before taking action, but even in a team which is relatively small compared to the Linux project, we do not always succeed, despite best intentions. And that's from people who are making an active effort -- people in other projects might not even bother with that. And just like with the CoC itself, there's plenty of potential for abuse if the person above you in the food chain is an asshole who doesn't like you. Even if their criticisms are invalid and can be disproved, should it really be upon you to invest the time and energy to do that if you're donating your spare time to a FOSS project? Personally, I just wouldn't bother in such cases and stop contributing. I have enough interesting stuff to do in life where I don't have to deal with abrasive nincompoops. So I suppose one of my main gripes with the term (not the concept, just the word itself) "meritocracy" is that it suggests a standard of objectivity which usually just does not exist. It's not a magical silver bullet which automatically leads to great results, but to many people (at least ones I've talked to), the word sort of implies precisely that (whether or not those people are correct in their assumptions is a different question of course). Yes, what we end up with in practice is sort of a meritocracy as well, as already said, but the term itself has very different connotations for many people. And as said: The CoC just by itself doesn't really ellicit much emotion from me. There isn't really anything in there which I'd consider spectacular news. If she uses it as a tool of power, then that's more of a problem with her and the people listening to her, less with the bare text, I think. Most CoCs could be used for that, probably including our own. Sorry for wall of text.
-
I haven't followed her closely enough to be familiar with her views and actions in detail, so I don't know what she personally advocates for. But I couldn't actually find anything like this in the actual new CoC itself. Am I reading the right document? https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=8a104f8b5867c682d994ffa7a74093c54469c11f I've read that document multiple times now, and honestly, I don't think it's very spectacular, or anything worth getting upset about. Unless I'm reading the wrong thing. IDK. As for your actual question: If my boss said to me "[Person X] is better because they are [part of minority Y].", then I would obviously consider that preposterous. But I don't see anything like that in the CoC. If the author of the CoC advocates for that, that's not really a fault with the CoC itself I think. But maybe I haven't found the right link or right document or am reading the wrong text, or have overseen a sentence or paragraph. Weirder things have been known to happen. It's easily possible that it's going to be badly enforced, but that's possible with any CoC -- even ours. It just depends on the mods, as @Sauron says. It's not a problem with the text, it's a problem with its application. In any case, most of the time, I try to stay way from FOSS drama -- too many fragile egos to deal with. My life's too short for that.
-
Feels great, to be honest. I even get paid decent money for it. More seriously though: My point is less that merit in and of itself is useless, but that most of the time when people go on about "meritocracy", they focus almost exclusively on the technological side of things, when in practice, whether or not you hold merit to a specific project is determined by many more factors. As said: An engineer with crappy people skills, no matter how brilliant on a technological level, would not fare well in the environment in which I work. They would be useless; i.e. without merit. Sure, what we end up with is a meritocracy of sorts as well. But not the kind of meritocracy of which your average internet dweller will think when they read the term, most of the time. I'm not saying my tech skills are irrelevant (otherwise I could be replaced by a preschooler, after all). But they're by far not the only thing which is required for me to be good at my job. So applying the term to my situation isn't very useful, because people are going to get the wrong idea. We need engineers with good people skills on top of good technological expertise where I work, otherwise we're simply going to fail at our mission.
-
As a side note on meritocracy: It sounds great on paper, but I've found it to be a rather useless concept in practice. Primarily because what "merit" is exactly in any given context is not as straightforward to determine a lot of the time and open to interpretation and ambiguity (at least in my experience). Example: I work in a relatively small team of engineers at my company, but we're involved in some EU and German research projects where you work with lots of people from other companies and universities. Beyond a certain baseline of technical competency and a will to work hard during crunch times, your people skills are going to be as important as your technological knowledge, sometimes even more so. You're going to be meeting new people all the time, and you need to be able to work with them without much fuss. Even if you're the most gifted engineer involved in the project, if you cannot play at least somewhat nice with the other folks on the team, you will be utterly useless to your company. In short: You will have no merit. The project will be far better off (and more successful) by hiring somebody who's maybe not quite as brilliant on a purely technical level, but can actually work with other humans. A meritocratic system based purely on technical aspects (for example, code quality, whatever that may be) would fail to take that into account. Another big thing is politics. Somebody has to secure funding for our engineering projects, either from within our company, or from outside. They need to be both knowledgeable enough on a technical level to know what can and cannot be done, and maybe even a rough idea of how, and they need good salesmanship. Often, this is a senior engineer (at least in the teams I've seen so far). They don't need to be super talented on a technical level -- they might have written rather crappy code when they were younger. But they're absolutely crucial in the grand scheme of things. So for me, any CoC where they mention a meritocratic system is a pretty big red flag, to be honest.






















.png)









