Why Memorize IP's When You Can Self-Host DNS Instead?
-
Topics
-
EzioWar ·
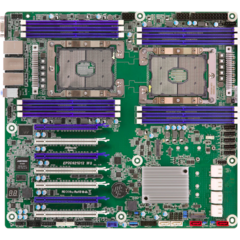
Posted in CPUs, Motherboards, and Memory0 -
1
-
WallacEngineering ·
Posted in PC Gaming0 -
Astrophel ·
Posted in Storage Devices1 -
2
-
Fat Cat11997 ·
Posted in PC Gaming3 -
Hax Traded ·
Posted in Graphics Cards0 -
Invincible Sugar ·
Posted in Peripherals2 -
ByteDisk ·
Posted in New Builds and Planning0 -
The_SlaY3R ·
Posted in New Builds and Planning2
-

.jpg.5cc14cacf0bfa9d58de316927a37ec08.jpg)














Create an account or sign in to comment
You need to be a member in order to leave a comment
Create an account
Sign up for a new account in our community. It's easy!
Register a new accountSign in
Already have an account? Sign in here.
Sign In Now