Search the Community
Showing results for tags 'vulnerability'.
-
Summary On October 2nd, 2023, ARM disclosed three security vulnerabilities for the Mali GPU Kernel Driver. The security vulnerabilities affect a significant amount of devices, and there are indications that one vulnerability may be under limited, targeted exploitation. Patches may not be available for all devices. Quotes On October 2nd, 2023, ARM disclosed three security vulnerabilities in their GPU kernel drivers. The security vulnerabilities affect a wide range of ARM GPU drivers, including multiple different architectures and versions. For specific information on affected drivers, please see ARM's Specifications Page. The vulnerabilities have been addressed in Android's latest security patches (2023-10-05 or higher). According to Google's Android Security Bulletin for October 2023, there are indications that one vulnerability (CVE-2023-4211) may be under limited, targeted exploitation. For more information regarding the vulnerabilities and security updates, you should check with your device manufacturer. Assuming, of course, that your device is still supported... Note: for Google Pixel owners, this vulnerability has been addressed in the September security update (2023-09-01). My thoughts I'm not an expert in this area so I can't say this with confidence, but it seems like a LOT of devices are going to be affected by this... including devices that are not supported anymore. Not only are Mali GPUs used by many manufacturers, the security vulnerabilities seem to be included in many driver versions. Look at their Bifrost architecture drivers, for example. ARM says that kernel driver versions from r0p0 to r42p0 are affected, and going by what's on ARM's developer page, that's every kernel driver before March 24th, 2023... and r0p0 was released in June 2016. Nearly seven years worth of drivers are affected, and who knows how many phones can't update due to discontinued support? Also, my current phone is a Galaxy S9+, which uses ARM's Mail-G72 GPU... which is based on ARM's 2nd generation Bifrost architecture... and Samsung doens't offer updates for the S9 anymore. Time for a new phone... I guess? Sources ARM Security Bulletin https://developer.arm.com/Arm Security Center/Mali GPU Driver Vulnerabilities Android Security Bulletin - October 2023 https://source.android.com/docs/security/bulletin/2023-10-01 Ars Technica https://arstechnica.com/security/2023/10/vulnerable-arm-gpu-drivers-under-active-exploitation-patches-may-not-be-available/
-
Hello, so about 1 and a half years ago I thought I found a sort of vaunerability with google maps and over the following months investigateted it further I will go into more details in a secound and would like a discussion and hear your thoughts but mainly I would like to have you informed about this issue because it could affect youreself. If I have spelling mistakes or my grammar is wrong please correct me English isn't my native language. I will update this Topic with mor detailed information when I get all of my notes together ^^ The "vulnerability" First of all I asked 2 companys which sad it isn't eligable for bug bounty so please don't spam random Companys with this article -thx When you are googleing a company or a location google will normaly show you the Google Buisness information that they gathered by helpful locals or websites so google is able to display the Information to you. The Problem is that (at least in my county Germany and I think in others as well) Buisnisses don't claim there Buisness on Google, that leads to the problem that -someone- could enter false Information. To be fair depending on how drastic your changes are to the data that google shows more people will have to report or confirm that information. I don't know how to programm a bot who could do that, but I have had time so I tried how much you could change and found this: Change the Telephone number by 1 number: 1 User Change the thelephone number by 2 numbers: 1 User (sometimes 2) Change the telephone number by more than 2 numbers: Changes drasticly from buisness to buisness but arround 10 Users with local guide or 18 without To change the website I think arround 5 Users have to say the same thing and the website has to have the buisness information. -I didn't focus on this as much as on the thelephone number why will be described in a secound. The Problem with chainging the telephone number: When a telephone number is active on a location/ buisness it takes about [2-8] months for the Claim your buisness function to accept verivication by telephone again. A Person with malishes intend could use a telephone numer and send every incoming call automaticly back to the original number so noby would notice that this would be the wrong number NOBODY CHECKS A WORKING PHONE NUMBER IF ITS "REAL" OR NOT The second you are able to verify via phone number you could turn the call forwarding off to recive the call and verify a buisness wich isn't yours. When you verivied that you "own" that location/ buisness you are able to cainge the information shown on google without confirmation That leads to one of the main vulnerabilitis: You can change the Buisness Website to a simular domain wich 1 Displays a fake website to grab Information 2 Have a cookie grabber and forward you to the real website you the user wouldnt notice The other main vulnerability is that nobody questions if the google bisnes owner is the real buisness owner so you could post events and discounts on the google page this would lead to a lot op upset custimers and a bad buisness reputation. The thired one is that [I think] you could record the calls that you would forward to the other number if you would connect them vai your server but I'm not shure about this last one because to be honest I don't have the tecincal epertise but would like to here from you if you are more skiled in this topic. How to protect youreself: You don't really have another choice as to claim your google buisness and check your data regulary This also apllies if you are not a buisness in case you are a cities office or something like that you may have to ability to take out the ability that people change your data but not shure (again) Before I posted this I talked to my local Police and a few buisnesses who are effected I can't contact all of you and I really want to make shure nobody will be harmed by this so I wanted to get the word out. If you have any questions or something like that feel free to ask I will make a reddit thread as well but its late and I probibly will post the link here tomorrow Reposts and follow ups are hoped for I you do I would love some credit ^^ Stay save Fabian
- 2 replies
-
- vulnerability
-
(and 3 more)
Tagged with:
-
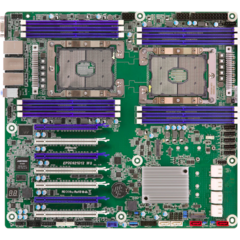
As an FYI as there are a few owners of Ryzen who should be looking out for the BIOS updates with the new AGESA 1208 to mitigate the vulnerabilities AMD just uncovered. I updated my Asus Pro WS X570-ACE running a 5950X and 2x 32GB Micron Rev B sticks from 4201 to 4304 with the new security mitigation fixes in AGESA 1208. Everything is stable but had to slightly reduce the aggression of my core optimizer per-core setting to prevent WHEA errors. Even with these subtle CO changes Cinebench R23 score is ~29K multi core and ~1680 single core which is similar to what it was on 4201 so seemingly no massive loss in performance following the update.
-
- security
- vulnerability
-
(and 2 more)
Tagged with:
-
Over the last few hours, Microsoft has announced they have patched a remote code execution in the Windows (server) DNS server. (CVE-2020-1350). There are already patches and workarounds, these need to be applied ASAP. You can find the article on the MSRC page here TLDR; If you cannot apply the patch you can quickly deploy a registry workaround which will mitigate the risk until you can fully patch it. HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\DNS\Parameters DWORD = TcpReceivePacketSize Value = 0xFF00 NOTE: this requires a DNS service restart. Edit: Specify that it only affects the server variants. Edit2: Take this with a grain of salt but there seems to be someone claiming responsibility for it over on twitter.
-
Source: http://thenewdaily.com.au/life/tech/2017/02/20/juice-jacking-public-risk/ Not a Ryzen thread! So how many people here use Airport power to charge their mobiles or appliances? I can see a reduction of people using power points or USB hubs at airports now, or people carrying more power banks with them
-
The CERT found a memory corruption bug in the Windows SMB Services (used for network sharing, i.e. file shares or printers, and then some). This can be used to crash such a system from afar by feedig it rotten packets. "Exploits are already publicly available.", says CERT. Microsoft has not reacted - yet. CERT suggests you block the SMB Ports to external networks until a patch from M$ is available. Read the full thing here: http://www.kb.cert.org/vuls/id/867968
-
https://www.bleepingcomputer.com/news/hardware/ssd-drives-vulnerable-to-attacks-that-corrupt-user-data/ While this may not give out your info it would sure cause a bad day for you when you lose your data.
- 4 replies
-
- ssd
- vulnerability
-
(and 1 more)
Tagged with:
-
DISCLAIMER: This is NOT to tell people how to break into people's networks. This is to bring awareness as to why people shouldn't use the default password included with their TWC(Now Spectrum) ARRIS routers. With that in mind. Let me explain the purpose of this post. Ever since my parents upgraded to TWC(prior to Spectrum overtake) our new router the ARRIS TG1672G threw me for a loop when the credentials were: SSID: TG1672GF2 PSWD: TG1672G17B6F2 Right in there: TG1672G-17B6-F2, Effectively 17B6 IS the password the rest is the broadcasted SSID. This was bad because checking other peoples ARRIS routers they were identical except for the SSID and the exact four characters used. For example: SSID = S PW = P Everybody's wireless password followed the structure: SSSSSSSPPPPSS, The location of PPPP doesn't change between routers. They're all the same. This was bad. It meant someone could custom dictionary attack the network after intercepting the four-way handshake (not hard to do) then test every possible combination within PPPP which is 36^4 (0 - 9 then A - Z) that means of every single router configured this way there's only 1.68 million (rounded up) combinations. A low power laptop could check that many passwords in under a minute. It gets worse. One day while troubleshooting my Ubuntu 16.04 installation which REFUSED to connect to my home network for a dumb reason I noticed something while checking the routers MAC address: D4:05:98:17:B6:F0 Do you see that? Let me display the WiFi password side-by-side with the MAC address: WiFi PW: TG1672G17B6F2 MAC: D4:05:98:17:B6:F0 Look carefully, do you remember 17B6 being the only "secret" part of the WiFi password? Guess what. IT ISN'T!!! ARRIS PULLED IT FROM THE FREAKING MAC ADDRESS!!! HOW STUPID IS THAT!?! I tested this with 5 ARRIS routers including my own. All of them granted me access when I inserted the XX:XX:XX:PP:PP:XX (P is the password) section of the MAC address. There is a FREE software tool called ACRYLIC WiFi HOME which is a wireless network analyzing tool (not a packet sniffer). It tells you the: SSID MAC ADDRESS!!! RSSI (signal strength) Channel (channels being broadcasted on 1, 6, 11 or 5GHz channels) 802.11 standard (b, g, n, etc) Max speed WEP security (if applicable) WPA security (if applicable) WPA2 security (if applicable) WPS THE ROUTER VENDOR!!! and some other information. Key things here. MAC address & the router manufacturer. This means someone living next door or someone pulling up outside your house has all the information they need to get into your network and even WPA2-PSK (AES) encryption can't do ANYTHING to stop it. CHANGE YOUR WiFi PASSWORDS IF THEY'RE VERY SIMILAR TO YOUR SSID's AND IT'S AN ARRIS ROUTER!!! Anybody could take over your network, spy on you, steal your information or just strait up shut you down.
- 13 replies
-
- security
- vulnerability
-
(and 3 more)
Tagged with:
-
While the folks at Bastille discovered this set of disturbing vulnerabilities about a year ago, as its holiday shopping season and I didn't see any info about this on the forums, figured this was a reasonable topic for a first post. Basically, if you are using one of a number of proprietary wireless connectors for keyboards and mice, you could be vulnerable to key logging as well as forced pairing. There is a nice website (https://www.mousejack.com/) set up to explain the guts if you are interested. One of the mice that saw special attention was the G900, which also exhibited a hidden key macro vulnerability tied to its programmable interface software. I imagine logitech's other wireless gaming mice have the same issue. Some of these problems can be fixed in firmware updates, but for others, the user is SOL because of poor design decisions by the manufacturer. The list of affected devices: https://www.bastille.net/research/vulnerabilities/mousejack/affected-devices Now the above list doesn't include other popular gaming wireless mice, but that may be due to lack of testing time. Best to check with the manufacturer.
-
Cylance has disclosed a hack that shows how vulnerable US election voting machines are. This hack has previously been theorized but this is the first time we can actually see it in action, on an actual voting machine used in the 2008 election. For me personally this just shows again why voting machines are a bad idea, but i already know loads of people are going to disagree on this. tom scott did a great piece for computerphile on why electronic voting is a bad idea. remember that this is just my and tom's perspective on the issue and do research and think about it yourself before pulling a conclusion from this. for a lot of people this election is one of the foulest they experienced, with reports even saying that the 2 main candidates are the least liked candidates ever. it feels like one giant mud throwing contest. some people have even said that voter fraud caused Bernie Sanders to lose the race to presidential candidate for the Democrats with this as source: http://www.electoralsystemincrisis.org/ in an article from cylance they describe the hack in detail and give some references to older researches on these specific machines they also described their proposals on how to protect voting machines against this type of voter fraud the specific hack requires the attacker to have an PCMCIA card, this card is then used to reflash the firmware on the voting machine in a very simple manner that can be done in under 10 minutes easily.
- 281 replies
-
- us voting
- voting machines
-
(and 2 more)
Tagged with:
-
An exploit has been discovered that affects A LOT of linux distro's. luckily there is an easy fix available that you can implement yourself quite easily. How to exploit this vulnerability? Give cryptosetup any password 93 times and a shell with root privileges pops up. So hold enter for about 70 seconds and you're in like flynn. What does this actually allow the attacker to do? The attacker can read or write anything to desire from or to the disk. the attacker can implement a script for later local user privilege escalation. Mitigrating against this attack is pretty easy, you just have to edit the boot configuration and add this: sed -i 's/GRUB_CMDLINE_LINUX_DEFAULT="/GRUB_CMDLINE_LINUX_DEFAULT="panic=5 /' /etc/default/grub grub-install sources: http://thehackernews.com/2016/11/hacking-linux-system.html http://hmarco.org/bugs/CVE-2016-4484/CVE-2016-4484_cryptsetup_initrd_shell.html
- 3 replies
-
- linux
- vulnerability
-
(and 3 more)
Tagged with:
-
Similar to what Google has done with Chrome OS, Apple has now published a patch for Safari and provided documentation on how to disable hyper threading on all Macs through Terminal. The OS update patches the flaw in Intel CPUs through Safari, and Apple recommends installing only Apps from the Mac App Store to avoid potential risks. However for users who use applications from outside the App Store and are concerned about these vulnerabilities, Apple suggests disabling hyper-threading. These security updates have been rolled out and are available to Macs running Mojave, High-Sierra, and Sierra. The following Macs are not compatible with the security updates due to Intel not providing the necessary micro-code at this time: MacBook (13-inch, Late 2009) MacBook (13-inch, Mid 2010) MacBook Air (13-inch, Late 2010) MacBook Air (11-inch, Late 2010) MacBook Pro (17-inch, Mid 2010) MacBook Pro (15-inch, Mid 2010) MacBook Pro (13-inch, Mid 2010) iMac (21.5-inch, Late 2009) iMac (27-inch, Late 2009) iMac (21.5-inch, Mid 2010) iMac (27-inch, Mid 2010) Mac mini (Mid 2010) Mac Pro (Late 2010) All other Mac's should be able to update and take advantage of the fix in Safari as well as the optional hyper-threading fix. According to internal testing, disabling hyper-threading can lead to up to a 40% drop in performance. It is rather unfortunate that Intel CPUs have been plagued by so many security vulnerabilities and the latest has resulted in having to knee-cap your CPU to nearly half of its performance just to fix the exploit. I can't help but wonder how mad Tim Cook and Dan Riccio (head of Hardware Engineering at Apple) are with Intel at these recent developments. All of this makes we wonder if anyone at Apple is looking into the possibility of building Ryzen based Macs seeing as they are currently not vulnerable to these security exploits that are massively hurting the performance of not just Macs, but all Intel based computers. I can't say I would mind seeing a Treadripper based Mac Pro or Ryzen based Mac Mini. Source: https://support.apple.com/en-us/HT210107
- 10 replies
-
https://www.overclock3d.net/news/cpu_mainboard/intel_has_revealed_77_new_chip_vulnerabilities_one_of_which_has_a_notable_performance_impact/1
-
Original article from UCR website Research paper: Rendered Insecure: GPU Side Channel Attacks are Practical Toms Hardware article about the vulnerability. From the University of California, Riverside article: So as of this time, the vulnerability is only known in Nvidia GPUs, however AMD and Intel have been notified to check. Nvidia will be releasing a patch, I just hope it doesn't require mitigation like the Spectre and Meltdown vulnerabilities did, however it seems a more straight forward fix.
- 6 replies
-
- gpu
- vulnerability
-
(and 1 more)
Tagged with:
-
Oh great. It seems, that the Logitech Driver Software called "Logitech Options" opens up a websocket without any authentication so it can be used by anything that gets access to it - being a websocket, code executed in a webpage in your local webbrowser is included. There is no fix so far. Logitech Options is the default software suite that all newer devices from Logitech use. The older software called "SetPoint" does not seem to be affected. Project Zero found this bug: https://bugs.chromium.org/p/project-zero/issues/detail?id=1663 German website golem.de has an article as well (in german, sorry... ? ) https://www.golem.de/news/logitech-options-logitech-software-ermoeglicht-boesartige-codeausfuehrung-1812-138218.html If you're versatile with system administration, you might be able to block this port via a firewall or remove the service in question. I did not try this myself, so removing the software entirely is the quick and easy way out. Stay safe, questargon
- 27 replies
-
Summary A new Bluetooth-vulnerability has been found, dubbed the BLURtooth, with so far no known way of patching it up. Researchers from The Bluetooth Special Interest Group reported the vulnerability, while it was confirmed by another group out of Carnegie Mellon. According to the researchers, the protocols that both Android and iOS follow when linking up to another Bluetooth-powered device - like, say, a pair of speakers - can be effectively hijacked to give an attacker access to any bluetooth-powered app or service on the phone. Quotes My thoughts Given the short range of Bluetooth, this doesn't seem to be a particularly noteworthy thing for your average consumer, but if you could e.g. hide a small, automated device next to a Bluetooth-operated lock or similar security-/authentication-installation, you could gain access to plenty of things you are not supposed to. On the other hand, this might even be beneficial to the hacker-minded ones amongst us, giving people a way of unlocking functionality in locked-down appliances, or to allow one to write 3rd-party software for such, without having to rely on manufacturers' - often rather poor - software. Sources https://www.bluetooth.com/learn-about-bluetooth/bluetooth-technology/bluetooth-security/blurtooth/
-
Hi everybody. A new UPnP vulnerability has been discovered recently that might be a hackers dream. It is listed as CVE-2020-12695 and got nicknamed "CallStranger". This security issue is serious, because the vulnerability is using an intentional UPnP protocol feature (Service subscription with callback) that is also implemented in many IoT devices which will NOT be patched. Additional information and links can be found in the article about the CVE above. Some more here: https://www.callstranger.com https://www.tenable.com/blog/cve-2020-12695-callstranger-vulnerability-in-universal-plug-and-play-upnp-puts-billions-of https://www.zdnet.com/article/callstranger-vulnerability-lets-attacks-bypass-security-systems-and-scan-lans/ If you want to know whether your local network has any vulnerable devices, download the python 3 script from this repository: https://github.com/yunuscadirci/CallStranger and let it scan your local network. It looks for all UPnP devices and checks them for "CallStranger". If such devices have been found, make sure that they can not be reached from the internet (i.e. check port-forwarding on your internet router) or turn their UPnP feature off! If the router itself is vulnerable, disable its UPnP functionality as well! You might even have to contact your ISP when you do not have full control over your router to check whether they can mitigate this somehow. The recommended patch for this is to only allow callback requests to the same network matching the URL of the subscription request. Routers and software running on common computers might get these patches soon™, but most of the cheap IoT devices will never. This means free DDoS carpet bombing for the internet villains. Or they can try to scan your local network using this reflection attack and get information that should not leave that network. Stay safe, questargon
- 18 replies
-
- callstranger
- upnp
-
(and 4 more)
Tagged with:
-
Summary A report by Check Point Research came out today describing a vulnerability in Amazon's smart home assistant Alexa. The vulnerability was shared with Amazon in June of this year and has since been fixed (why the report was just published). The vulnerability gave hackers the ability to add or remove skills, get a list of the added skills, get the user's voice history, and get the user's personal information. All that was required was having the user click on a link sent by the hacker. They would then be able to do everything listed above. The most significant of which are access to victims voice history which could have sensitive information like banking info in there and to see all the information on the user's profile including address, email, and phone number. Quotes My thoughts I'm glad this was found by a research company and not after being used by a hacker. This is why we dont click on random links people! Good thing Amazon was able to fix this in just a few months and not a few years, leaving it open and leaving users at risk. Sources Check Point Research Report cnet
-
So as it turns out, a bug in Twitter's hashing process has led to millions of passwords being released. http://money.cnn.com/2018/05/03/technology/twitter-password-bug/index.html While it's doubted any passwords were stolen, this is still a massive security breach. Thoughts?
-
E-Fail is a vulnerability found by German security scientists and may concern a lot of people that use encrypted e-mail services. The EFF has released its knowledge around E-Fail, how to react and how the security flaw works. Nice read in my opinion: https://www.eff.org/my/deeplinks/2018/05/not-so-pretty-what-you-need-know-about-e-fail-and-pgp-flaw-0 For thise who don't like long articles: Be safe and know your encryption!
-
VPNFilter malware - Cisco's Talos finds new network gear vulnerability Cisco's Talos Intelligence group shares their findings about a new multi-stage malware they found on network devices in a blogpost. The post summarises the different stages of the malware, manner of infection, malware activity, and how to protect your devices (if possible) against the threat. The below information can also be found on the blogpost itself: https://blog.talosintelligence.com/2018/05/VPNFilter.html Brief Technical Rundown Stage 1 Stage 2 Stage 3 Defending agains the threat Update #1 The FBI released a Public Service Announcement regarding the VPNFilter malware. https://www.ic3.gov/media/2018/180525.aspx
-
https://www.theregister.co.uk/2018/02/09/netgear_security_patches/ I'm surprised no one has posted about this, yet. A group called Trustwave have been researching vulnerabilities in Netgear routers for the past year, and they've found several of them. Multiple models are affected by various issues, ranging from password bypasses to the ability to run code with root access.
-
Hi, I have a Gigabyte z370M-D3H Motherboard with F3 BIOS, "recently" many manufacturers released BIOS update (Gigabyte released the F4 BIOS) because of the Intel ME vulnerability and I was thinking in updating the BIOS. But the were some warnings in Gigabyte website and some people saying that flashing (updating) the BIOS can be risky and shouldn't be done unless there's system instability. I'm always careful of what I install and where I browse in the web + have an antivirus + check the PC with other portable AV. How this Intel ME vulnerabilty works? Does the attacker need to make me download a Trojan or other malware in order to exploit it or he/she doesn't need any and can just acess directly? It may sound like a noob question but I'm sorta paranoid and I'm afraid of installing a new BIOS just to screw a new motherboard that was working just fine and could have prevented this vulnerability just by browsing carefully. I apologize if there's already another topic about this but I couldn't find any.
-
I found out about this recently and I'm no expert but it looks really bad. Very sneaky of them to have, what looks to me, like a perfect backdoor disguised as a feature for big companies . Apparently, it affects everyone who has an intel cpu 6th gen (Skylake) onwards. Here the link to intel's detection tool. And this is intel's official response with all the details, affected systems and detection tool, etc. I unfortunately have a 6600k+Z170 Pro Gaming, so I'm going to have to update my BIOS to fix this. Atleast that's what the update tool from Asus is telling me to do. What a mess, I really don't want to brick my system for this. https://arstechnica.com/information-technology/2017/11/intel-warns-of-widespread-vulnerability-in-pc-server-device-firmware/
- 4 replies
-
- intel
- management
-
(and 3 more)
Tagged with:
-
Hello LTT forum. Came across this article by Github user "indrora". I feel that this should be shared with more people since it makes any computer with LiveUpdate installed very vulnerable to attack. https://gist.github.com/indrora/2ae05811a2625a6c5e69c677db6ea331 The simple solution is to just uninstall LiveUpdate from your system. The biggest problem seems to be the fact that LiveUpdate is preinstalled on many laptops that come with Asus hardware. Please note that I am not the author of this article. I have only signed up today in order to share this article, I rarely participate in forums.
- 13 replies
-
- asus
- liveupdate
-
(and 2 more)
Tagged with: