Search the Community
Showing results for tags 'nsa'.
-
This can actually useful for some purposes out there that isn’t malicious, I still don’t understand why they massed it t ope-source, something like this with the wrong hands could be bad. This is actually pretty smart if they are using it to recruit people. There’s plenty of people with unused talent out there, this maybe their chance to prove themselves. Let us know down below what you think, is this a good thing or not? What could this be used for? SOURCE
- 45 replies
-
Source https://rbt.asia/g/thread/62641401/#62645883 I found this on the r/pcmasterrace subbredit and I thought that it should be posted here too. In my opinion this is an awful thing to do and I think that they are going to be really hurt in the long term from this move.
-
Sources: Ars Technica, Reuters, BSI (Germany) The WaPo article reporting the same events is here It adds additional details about the role Kaspersky AV reportedly played in identifying the NSA material the employee stored on his home computer. In a statement, Kaspersky Lab officials wrote: This is a bit concerning. I've used Kaspersky AVs since college when my PC got infected by a nasty worm that hid all my essential files and replaced them with shortcuts and stupid Microsoft Security Essentials wasn't able to detect and remove it so I downloaded a 30-day trial of Kaspersky Internet Security and it detected the nasty worm and I was able to recover my files and from that day on, I've been a customer and I even installed it to my parents' PC at home. While I don't think home users have little to worry about, it is what the alleged spying it does. Until the US Senate hearing ensues, I'd still give them the benefit of the doubt unless the code inspection by US CERT and NIST found something deplorable. Founder and CEO Eugene Kaspersky responded to the allegations in his personal blog saying: I don't know if I'm buying Kaspersky's response there. But the crazy thing is that Israeli hackers penetrated inside Kaspersky Lab's own network and remain undetected for months just to know the shenanigans of the NSA but only to see that allegedly, Kaspersky is working hand in hand with the Russian intelligence. It does raise a lot of concerns but the caveat is that a lot of these evidences proffered against Kaspersky are unknown sources. I think Kaspersky is caught in the middle of a modern day cold war but doubts on cyber espionage cannot be ruled out until the 25th of October when Eugene Kaspersky himself will testify on the US Senate. In their company website, they explained how they work and how their cloud services protect user privacy which you can read here and here.. You be the judge. I'll just wait here as the story unfolds. Although reading their privacy statement on their cloud protection service, I kinda wish Microsoft would finally allow full disabling of telemetry in Windows 10. Maybe they'll finally add it in their Spring Creators Update? UPDATE: There was an Ars Technica article at the moment about how allegedly Kaspersky modified their AV to be used by Russian intelligence to steal NSA secrets. In the latest Reuters article, Germany's BSI federal cyber agency said that the malicious accusations to Kaspersky Lab have no evidence that the Russian government used Kaspersky Lab AV to spy US authorities. Here's the original press release from Germany BSI in the original German language. Any German member in LTT can translate it correctly: Is Google Translate correct in translating? I hope so. But I want to know on what grounds or how did the German BSI investigated and found nothing. If Germany is correct, then all of the allegations to Kaspersky Lab and Eugene Kaspersky is basically oral defamation due to geopolitical conflicts. I wish other intelligence agencies from other countries to come to prove or disprove the allegations.
- 19 replies
-
- cybersecurity
- anti virus
-
(and 3 more)
Tagged with:
-
Looks like there is another silent NSA hack called DoublePulsar that allows the taking over of the kernal. The piece is a bit of a fluff but its got some interesting bits. https://www.nytimes.com/2017/06/22/technology/ransomware-attack-nsa-cyberweapons.html
- 4 replies
-
- doublepulsar
- nsa
-
(and 1 more)
Tagged with:
-
But why Microsoft? Source: Ars Technica UK, Microsoft (Windows Blog) But why? I thought Windows XP is already unsupported? Wouldn't that hurt Microsoft more? You think that Microsoft is doing this for the benefit of their customers, I beg to differ. I see this as indecisiveness. Apple is true to their word when they declare a device to be unsupported. Here's a commentary from Peter Bright from Ars Technica as well: Not to mention, they're not doing their latest OS Windows 10 any favors. Windows XP is a 32-bit operating system released in 2001 and it makes no sense at the moment to keep patching it. Just look at Apple, when they decide to stop supporting an OS or an old device, they do. Do you see Apple still releasing patches for an old iPhone 3GS or a 2008 polycarbonate MacBook running Mac OS X Snow Leopard at the latest? No.
- 185 replies
-
- windows xp
- security
-
(and 3 more)
Tagged with:
-
EternalRocks, a new variant of malware leveraging the previously NSA-hoarded vulnerabilities that were dropped by the Shadow Brokers, has been seen making its rounds in the wild. This one could be a bit nastier than the big WCRY/WannaCry malware that blew up recently in the way it spreads. It uses the DoublePulsar, ArchiTouch, and SMBTouch tools. "Miroslav Stampar – a member of the Croatian Government CERT and author of the sqlmap tool used to detect and exploit SQL injection vulnerabilities – detected a new worm that exploits Windows Server Message Block (SMB) vulnerabilities. He named it EternalRocks and said it uses six SMB-specific NSA tools to spread, whereas WannaCry used only two to infect hundreds of thousands of computers across the globe. " "At this point, the malware doesn’t appear to be dropping ransomware or any other payload. But it could be paving the way for a future attack. " https://nakedsecurity.sophos.com/2017/05/22/after-wannacry-eternalrocks-digs-deeper-into-the-nsas-exploit-toolbox/ https://github.com/stamparm/EternalRocks Bottom line, keep your security patches up to date and use some common sense when it comes to email attachments.
-
The reason behind the bill: According to this article, the law might help companies like Microsoft updating our computers with security patches due to the amount of vulnerabilities they are finding. This is the bill they are trying to pass: Even if there will probably be no-one to enforce this bill, I hope it does help M$ and other companies to secure their piece of software... Edit: fixing the post to fit the community guidelines @Energycore
- 16 replies
-
- hacking tools
- nsa
-
(and 3 more)
Tagged with:
-
source: https://www.theregister.co.uk/2017/05/16/microsoft_stockpiling_flaws_too/ hold on to your tinfoil hats because this one is straight out of a Stanley and Laurel movie get this: these mofos knew about the exploit and build the patches since February - you wot m8 what the fuck! if anyone got hit by the Wanna Crypt ransomware and lost important data or had to shut down services, sue these motha'fuckers
- 87 replies
-
So, I have a project for English class where I need to design a poster that illustrates the negative effects of mass surveillance. There are many examples of these posters online, but I am trying to make something unique. I was thinking of making something that has a prism with light refracting through it, to stand for the NSA PRISM program, and maybe have the light rays represent different spying programs. Is this a good idea? or does anybody have something better? I am a little bit low on creativity when it comes to making artwork . Something similar to this, with the white light representing the broad data collection? and maybe the refracted light beams representing more specific things, maybe sort of in order of a timeline (red through violet) like this: https://projects.propublica.org/graphics/surveillance-timeline I also need to embed enough meaning in this poster to write a 600 word mini-essay about it, but still keep the entire thing rather simple, to make it easy for somebody to read it, and remember it at a glance.
-
https://www.washingtonpost.com/world/national-security/prosecutors-to-seek-indictment-against-former-nsa-contractor-as-early-as-this-week/2017/02/06/362a22ca-ec83-11e6-9662-6eedf1627882_story.html In an update to a story that broke last year, we are learning more information on just what it was that former NSA contractor Harold Martin III stole during his 20 year career with the agency (and/or affiliated agencies/departments). Among the thousands of pages that were found hoarded in his car and home, he also stole 50 terabytes of data, including more than 75% of the Tailor Access Operations' (TAO) toolkit. If you aren't familiar with the TAO, they are responsible for creating and deploying "software used to penetrate foreign targets’ computer networks for foreign espionage purposes." (They also likely wrote Stuxnet, Duqu, Flame, and whatever else we haven't discovered yet.) This story is heavily tied into the recent history of surveillance disclosures and state-sponsored hacking, but here's the quick version: NSA/FBI increased efforts to identify leaks after Snowden revealed what they had been up to, Likely due to these increased efforts, they find a long-time employee has been hoarding massive amounts of classified information in his home and car. Seriously, they say stuff was just laying in his car and all over his house. And by massive amounts I mean this was the largest theft of classified information, and it took place over 20 years. Not much is new in this story, we knew he stole thousands of pages and 50 TB of *stuff* back in October, but we're just now learning that it did, in fact, include almost the entire digital arsenal of the NSA. He has been held pending trial since October. Federal prosecutors are set to press charges next week for theft of government property and unauthorized removal and retention of classified materials. Full complaint here What makes this story different from the government related espionage stories is that it is difficult to tell if Martin's theft was malicious (or intentional) espionage or simply hoarding. And that's what I wanted to talk about today--Do you think it matters? If you want to chime in I'd urge you to read his Wikipedia page, it's brief but impressive. He is a highly educated military veteran with a long career in government. If this really was an incident of hoarding--an obsessive compulsion to collect all the data so that he could do a better job (as his defense has claimed)--should the government take some responsibility? After all, they granted him TS-SCI clearance. If he is a hoarder, surely they would have discovered evidence of this during background checks. P.S. I got really distracted writing this so it might be all over the place, but if you made it this far, take a look at this cool tool from Kaspersky that tracks APTs.
-
Source Friday, January 27, 2017 | By Elizabeth Banker (@elizabethbanker), Associate General Counsel, Global Law Enforcement [21:48 UTC] https://blog.twitter.com/2017/transparency-update-twitter-discloses-national-security-letters Transparency is important, this is too little too late. It's important to keep in mind these are just gag orders were lifted on expiration, not by new administration.
-
I'm trying to learn more about how effective a VPN actually is vs super-power govs, ISP's, major tech, or anyone with an unlimited budget. I would like to know about the different encryption used and how long they would take to break. My options are listed here <https://support.hidemyass.com/hc/en-us/articles/202720306-VPN-Protocol-Comparison> Is communication from US to another counties VPN server in the tunnel caught in NSA fishnet as I expect but only that it is encrypted? general ways to make it harder to be tracked. Ex. Set my IP location to automatically change every X number of min and use features like Secure IP bind so programs cannot access the internet without the tunnel ect. I've taken steps to make sure I'm not leaking my IP via https://ipleak.net/ and https://www.dnsleaktest.com/results.html. Any other tests I should run are most welcome. If anyone has a good suggestion for a DNS that would be welcome too. Something preferable that has user privacy at its core.
- 15 replies
-
Well now, grab your tinfoil hats, or make some if you don't have one. Source: http://www.zdnet.com/article/us-spy-court-didnt-reject-a-single-secret-government-demand-for-data/ So, tell me again, you have nothing to hide? What does it matter when you don't know, and don't have any form of legal representation WHAT-SO-EVER? Discuss.
-
So. Well there's really no nice way to say it, the FBI no longer needs a warrant to investigate people. Why? Because the NSA doesn't have to get a warrant to spy on people, and the FBI can look at anything the NSA uncovers. Without a warrant. So basically, they only need to have "national security reasons" for the initial collection of your data, after that, they can look through it for any reason, without a warrant. Source: https://www.eff.org/deeplinks/2016/04/secret-court-takes-another-bite-out-fourth-amendment
- 33 replies
-
source: https://www.theinformation.com/inside-apples-cloud-infrastructure-troubles? via: http://arstechnica.co.uk/information-technology/2016/03/report-apple-designing-its-own-servers-to-avoid-snooping/ this is crazy bananas ... or is it they've already done it with HDDs, as per Kaspersky report http://www.reuters.com/article/us-usa-cyberspying-idUSKBN0LK1QV20150216 and even routers: http://arstechnica.com/tech-policy/2014/05/photos-of-an-nsa-upgrade-factory-show-cisco-router-getting-implant/ this also ties in with the news that Apple wants to design and implement their own hardware in datacenters: http://venturebeat.com/2016/03/17/apple-cloud-project-mcqueen/ the US Gov - a shitshow of biblical proportions; add Donald Trump to it and will implode I wonder .. where does it end?
-
GCHQ rejected encryption standard because it was too good
Oshino Shinobu posted a topic in Tech News
So, as we all know, various nations' intelligence agencies have been spying on their populations for quite a while now. Most notably the NSA in the US and GCHQ in the UK. These agencies have been pushing for "stronger" encryption on face level, but the options they are trying to push are actually designed to have massive backdoors to make it easier to spy on those using it. For those outside of the tech community, it's easy to not know what encryption standards are actually good, especially when the agencies pushing them are flat out lying about how secure they are. For encryption standards for devices such as smartphones, which we now store huge amounts of personal and sensitive data on, it's extremely important that they are secure as possible. The government wants to watch what people are doing more easily, so they want to push encryption standards that make it easier for them to spy, which in turn, makes the encryption standard easier for non-authorised (wouldn't consider the government authorised in the first place) people to break. A document from 2010 has revealed that the GCHQ analysed a proposed encryption standard, MIKEY-IBAKE, but turned it down, quite literally because it was too good and made it harder to gain access to the public's phones without them noticing. Instead, they pushed (and still are) the MIKEY-SAKKE standard of encryption, which has built in backdoors for intelligence agencies to tap into mobiles without their users noticing. The most worrying part about this is that it's being marketed as a more secure method of encryption, despite it being full of backdoors, literally making it easier, by design, to break into. GCHQ, UK. It's disturbing how much the government is blatantly lying to the public, despite constantly being called out on it. A lot of publicly viewable discussions on the matter, between MPs and industry experts make it clear just how little those in power understand the areas that they manage. It's about time that experts on the matters of encryption, online security and laws are put in positions of power within the government, rather than politicians who have to be given the watered down explanation, making it extremely easy for them to be convinced by intelligence agencies. Links: Source 1 Source 2 Steven Murdoch's Report GCHQ IBAKE Analysis- 10 replies
-
- encryption
- mobile
-
(and 3 more)
Tagged with:
-
According to The Independent the recent Paris attacks perpetrators used PlayStation 4 consoles to communicate and plan the attacks. The article goes on to say that intelligence services are unable to spy on these communications due to the encryption employed. So my question is this: Will the NSA and GCHQ start looking into ways to circumvent the encryption thus allowing them to spy on all gamers under the guise of national security and what effect will this have on civil liberties and personal information? The Independent article: http://www.independent.co.uk/life-style/gadgets-and-tech/news/paris-attacks-may-have-been-arranged-on-a-playstation-4-reports-claim-a6736231.html
-
Once again having issues with privacy... http://arstechnica.com/tech-policy/2015/10/court-says-its-again-legal-for-nsa-to-spy-on-you-because-congress-says-its-ok/
-
The top EU court today ruled that the privacy of EU citizens isn't adequately protected in the US. This ruling invalidates the "Safe Harbor" agreement of 2000. As a result, data from EU citizens may no longer be stored on US servers, where US intelligence agencies have access to it. The technology companies will have to review their data protection policies and start fresh negotiations with the European privacy commissions before they would be allowed to store data on US soil again. Source: http://www.pcworld.com/article/2989735/eu-us-safe-harbor-agreement-is-invalid-court-rules.html My original source (in Dutch) : http://deredactie.be/cm/vrtnieuws/cultuur%2Ben%2Bmedia/media/2.37414?eid=1.2462056 Personal opinion : While this could be considered a victory for the EU citizens, it's only a hollow one. While the companies may not store the data on US servers anymore, nothing stops them from letting it pass through those servers, leaving plenty of opportunities for the intelligence agencies to scoop it up as it enters or leaves the US. Also, nothing stops GCHQ from scooping it up in the EU and then sending it to said US agencies for "national security reasons"
- 9 replies
-
- eu-us
- safe harbor
-
(and 2 more)
Tagged with:
-
https://www.hackread.com/canada-looking-into-windows-10-spying/ Canada to the Rescue! I'm glad someone is finally taking up this issue, the problem with Microsoft's "Users can turn our crap off" is that turning the crap off doesn't change anything at all, it only says it's off. I think anything regarding a user's information should be private by default, well that's kinda impossible, in 40 or so years we'll have PCs built into our body along with that comes spyware and ads and ad-blocks and malware, maybe even paralyze or killswitches.
-
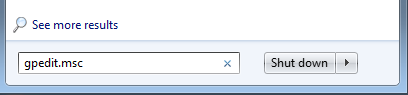
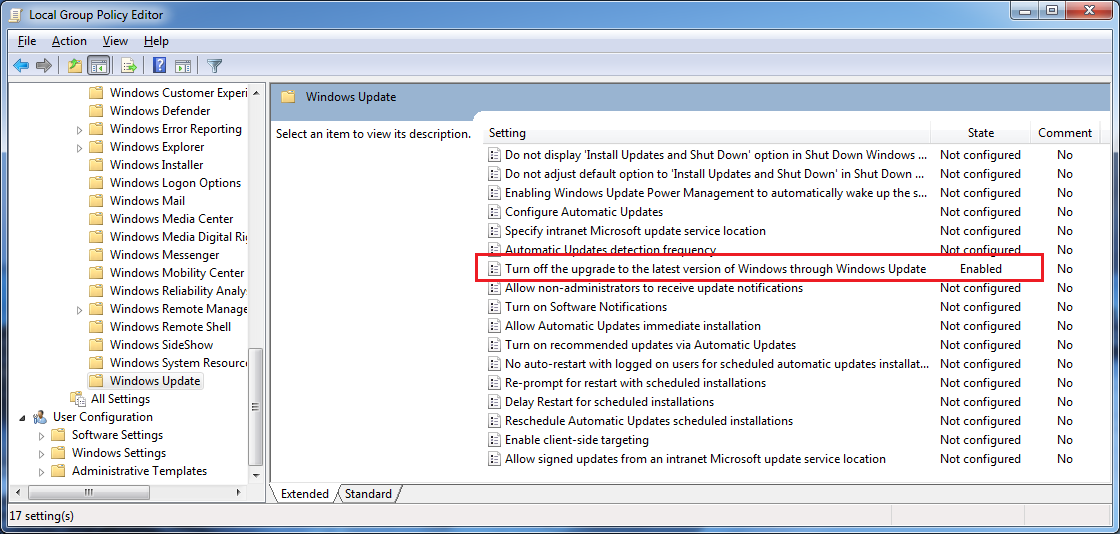
Step 1: make sure you have win7 pro (or win8.1 pro?) and not home-premium. If you have home-premium, then close your browser and cry yourself in a corner. (Or install Arch Linux instead, your choice.) (EDIT 10-Sep-2015: if you have home-premium (or a "core" version of win8...whatever that means), you might still be able to edit the registry to "suppress" the win10 offer; so if you do, skip all the way down to my post below for more details.) Step 2: make sure you have (mostly) all the security/important windows updates installed, especially the newest "WU client" update (like this one). "Optional" updates can be left alone. Step 3: make sure you're logged into Windows as an administrator and open up the local group policy editor, easiest way to do it is type "gpedit.msc" in the start menu text box like so: ...and hit enter. (Don't ask me how to find it in Win 8.1 without the start menu because I have no idea, just "search" for "group policy" and it should be the first result.) Step 4: now in the local group policy editor, navigate to the following: Computer Configuration -> Administrative Templates -> Windows Components -> Windows Update Step 5: now in this folder double click "Turn off the upgrade to the latest version of Windows through Windows Update" and then click "enabled" then hit ok. Final result should look like this: Close the editor and now Windows will "never detect, download, or install an upgrade to the latest version of Windows" (aka win10+.) Source KB article. Have a nice day
-
:mellow: I wanted to see how the "New Horizons" mission was coming along and came across this download site from JPL. I'm a little spooked about files and Windows right now because of the recent Adobe scare and how they still need to patch their 0-day vulnerability (as of 8 July.) The recent outing that the FBI was a paying customer of Microsoft remote-monitoring spyware called "Galileo" is making me paranoid about using Windows in general, because they can still do whatever they want (Quis custodiet ipsos custodes?) and still call it the "Freedom Act" since it recently passed right? Is it time to just install FreeBSD over Windows and call it a day?
-
Check out these digits: 31A7 0953 D8D5 90BA 1FAB 3776 2F38 98CE DEE9 58CF Facebook now offers the option to encrypt all email notifications sent to you with a public gpg key you set in your profile, and sign all of their emails to you with their public key. These two steps should ensure that; 1. Nobody but you can read the notification emails facebook sends you. 2. You can verify any notification email as coming from facebook, against the current operation key they are using (which will in turn be signed by their primary key) Adding your public key to your profile will also make it show up on your profile. If all of this seems like gibberish to you, the EFF has a pretty good explanation of the technology here: https://ssd.eff.org/en/module/introduction-public-key-cryptography-and-pgp It seems that facebook want to continue in their quest to have all of your data, but make sure nobody else has it. (unless they pay :^) Source: https://www.facebook.com/notes/1611941762379302 -----BEGIN PGP MESSAGE----- Version: GnuPG v1 owF1VgtwVNUZToKvbENrqQ3FR+eIw2ua3c0mwG6SOk7eiSgEs7Ri1PbsvWf3Hvbu PTf3nJvlgjJWY4PjWMBHx8JUbRAHRcQxIh0LClMQaKviCLZqKYw1UhWiFqLDY6D/ OXd32bQ0szPZe8/5//P93//939mV48eVlJV+++GWed8ER0ZK//x5omSB+eJVzQbR 0oi5AgmDcIJ0mqKC16PaSGMUVdfNqkUtsZZZqK66qRFF2hqbUG00OhvVtNXGUF2s uRW1tLbWoVmx5rZAINBDM6k7DCHs+nCYhuDBdUIay4RvriZ1TQkvZFupnrDcEwi0 YY0kGEsji2URSyaJwyUAxGxBmYUEQ8TSHM8WCJsmIhlMTdgqaJJqWO7giBNLyH0e c1GWCgNhZLsJk2ooZadQmnhqhROBqCW/Osh2WJKapAphS0ecpiyVmyXlwdTxD+Fj UvoLubSQMhSIK5JEliEuiA0oDOaaOoDlrgPvDSwaAoFICM1lCaZ7KAG8ymwatpBD sK5qLK4jf2oyzweUpXMZEwrUhNDCXGwfcWjSA+DeBaIR5ghoplYKJR2WKeSCQlOY Wly1Fmmu40jKmE0cP1hyBCuQFqC7XMZPzxpUM6B4IAZoE65joQRRZBEdJbw8Iw7N YMeTGWZA3xt1XQb7JBfIyjFZ4N3Pik3OUAanCaJCspdFro3Y2A6F/r+UauOpljiO Fksp0NPrMkHu6BTTuCTKQzRjM0dgXx8uV21RHNiE2RKIIV8TVBBhkhATcZwkShqS cOG4ijc/EErWmGURLS/OQiSVQgRqSQNKMgdJtrGlSSXACnyyhoeyBDmuVZRBiUzW y6kAyQNm1BGPd3X7ouvojncrHLlYIKWP6gANxeEEZkkIKlAeWFRRNlcwsRYxz0dF hYdSLnZghRAOnfSYJTXIoHg1dH5T1eGhQAfLEonFNwJBNMNiJktRiAQM8AzisUyl AbAJRz4X15SDonpbRFEIdfkLqvMQRWgfNN8C9Blfh0q00CZFhGZgSAkTwV0QIihb STyEfmrAmIjzxHNC0opHn/7/ZlfJyZ+OHH+Oz278pu4qVQEXTJYPcUKNRTLHS4Zw jlNQcwZ7UvtY0+ANTcgKoEgTJkqQxQJGRZmOEFgzMpCBz5DnwoQyy++HH0j4BbGw /BvYxVxLgLPIzhk58ciu0z6seT4umqMhjxYqYDpW6pCzm3Kw7oKXechhpilHUfo5 qJgshmGnEh0G+yRZEDoWeaOC4zBUVWicRK/raJ5NrK72rqJBVoTmB18NaENOI2pR jktCGgiwCRsng4EFBQvCv8kFE7+Q5SkDV70vNPW8YxAQp2zPGJJ4QUuyN0pPmsFk 06QODElFHr1CppKPAV7li4D5YpAsKRIkZTmocOaYewa8aKG6DsC7pBoSPlOurWMY QYWWZa0itqpyVoqRTnhaMBslHJblxAE7FvUBBH/S1zgYWzabDeXNWrlbhoRxAlDd wH0pXy/7jTURlOMCRhf2nS4Q6Eyev7uUBZEMRyaFyUvRRAJ6zo0cmb7YW9vakAHy xZJaIV2Bse1ClwIxseW3xb8Iz8+9hwwwiPoCWs71EEkmQ8xJhYkVzjDdNUkYpsGB bwpu0GchCCwEFZkMlGkbXhDcLGinbMAtcliVAAuXXt66ZLnUcom6e1Tfel3C1ZKB +0i+ZsU68I+r1AWrHEfdv5Z/64J9EFUuFSE03bVA5Ny/6WzQTf2d8s7qhhxaUXX/ 0wtQAeHhyOxIpG5mJDq7pjZaV1tdE3ig7OqLSkrLSi65uEz+fCoJlF+e/001eeZ3 zi1Zs/Ivj28c7V2cTD+bPH6CHTl8t/XpvXOenV/2zUtXL1s7da6xrXLnqHHF1/P+ ldm8o3pg5Pq3b1n44MTggUUffNV005ovHts7/NQL9x178qNHfrH1haEjS89uuvyL U/qQMXXiuhVzl76/9svB1nd73nzq+yefmTTxTJqvov2bn7uq/OV7FuzZYTUcWzX5 gbP7+fbPSUUmXH64srRnzoSnD/x6aEiLLY8sbx/9YPTaLacH5hwdeuOW5zt3fZj6 +sCDHaUVW1Z9/N1V5Us+2nlprOfnS1PrywcGFp97hrdHX981/DFbdij2t070xPLf /jX7s/6DFYv2773m+JWD6c7HBrefHD4S++Otv1rWNe79dxpH26sfLx148/YbdvcO v9UQ+cn81+IN9/59/r4V8Z1d66r2nLjr0W+9uGNj24+3hN++nUwZid7z77s/ib6z 7+RL0zb0Hbiu8vVjIv27+2sum3CYV3csOd2w+tyPTg9Or5hZX7lpypw2fcorFZnf LJu3evvKQ+HRwyseGnji5emvvnen+YdtqyfsWHtX+4w+un9N6+7Z65+cv/7GyoOT PhshmZsv+oF1aMEvB49/1t+/nGyaqfXe1lW74Yx56tS0PzW92z/uwxXj/9Gz4Xvk tYcCV3751TW7m7vHb9w3PPLp1JZd0V3Vt01t3muKDvTemTceLrt423Ox0vu2jiys P7vz2k/Grxl+64p1/3zkRNfv1046eqO7+SC65OirWy/b8+j6H/4H =mfqb -----END PGP MESSAGE-----
-
The NSA's domestic surveillance program expired at midnight after the Senate failed to reach a deal to pass legislation Sunday evening. The expiration came after the Senate convened for a rare Sunday session to deal with the expiring provisions of the Patriot Act. Before adjourning without reaching a deal, the Senate made some progress, clearing a key procedural hurdle on the USA Freedom Act, but due to procedural objections by Sen. Rand Paul, the Senate was unable to hold any additional votes to move forward with the measure. Three key provisions of the Patriot Act expired at midnight -- Section 215, which authorizes the NSA's bulk collection of Americans' phone records; a roving wiretap provision that allows law enforcement officials to monitor terror suspects that use multiple phones; and a program that officials can use to monitor "lone wolf" terror suspects, not connected to any known terrorist organizations. The NSA started the shutdown process at 4 p.m. Sunday. It will take an entire day to reboot the system, if Congress passes legislation reforming the metadata collection program. Senators returned to Capitol Hill Sunday afternoon, just hours before key provisions of the Patriot Act, including the NSA's controversial bulk collection of American's phone records, were set to expire. The Senate cleared a key procedural hurdle on the House-passed USA Freedom Act with a vote of 77 to 17. But objections by Paul, R-Kentucky, delayed further votes on the measure. Senate Majority Leader Mitch McConnell originally opposed the House-passed USA Freedom Act, but Sunday, he said it was the only option. Legislation allowing mass collection of phone records expired Sunday Patriot Act also enabled wire taps and warrants issued without evidence Senate tried to pass reform bill but was frustrated by Rand Paul (R-KY) Paul claimed victory, but admitted replacement law is likely to be passed Head of CIA now warns terrorists are 'watching developments carefully' and says ordinary Americans at risk because of political grandstanding Source : http://www.dailymail.co.uk/news/article-3105089/Senate-makes-ditch-bid-extend-NSA-s-bulk-collection-phone-records-Rand-Paul-swears-block-legislation-let-Patriot-Act-expire.html http://www.kitguru.net/gaming/security-software/jon-martindale/us-phone-tapping-clause-expires-nsa-halts-servers/
-
A Member of the Austrian Parliament (Peter Pilz) posted some pictures from a construction site near the United Nations Office in Vienna on Twitter. There have been strong indications in the past, that this site is used for the observation of mobile phones by the NSA (which of course is complelty illegal to do so in Austria by a foreign intelligence agency) Apparantely the US embassy wasn't to fond about him posting that pictures showing the US-intelligence company Michael Baker working. ____ It is kinda ironic, that the US embassy is demanding privacy for their employees while building a site to invade the privacy of every Austrian and many other Nations working in the United Nations Office in Vienna. left the United Nations Office, right the IZD-Tower with a small hut on top hiding NSA equipment.


.thumb.gif.6c208fabb86f0f3f5be1b0ccf62fe67f.gif)



.png.76ca6e4214773d3c398cf50c0416c9c1.png)
.png)